
In what may be the first large data breach of 2019, Houzz just issued emails to their customers about a data breach that occurred in their systems in December of 2018. I happened to be affected by this matter and felt it would be beneficial to my followers to share the news as well.
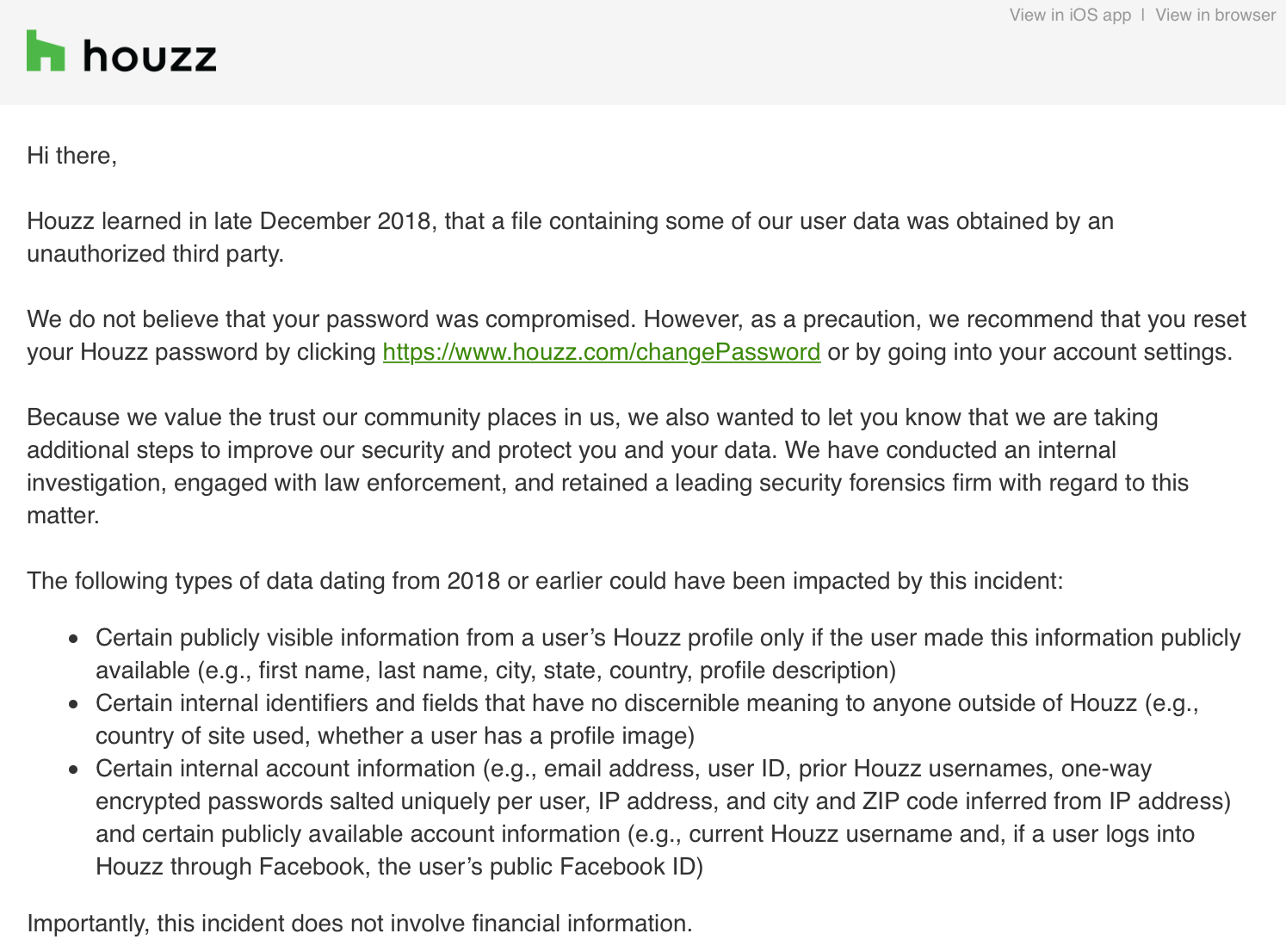
While Houzz is saying that financial information was not compromised, the following information was obtained by an unauthorized third party:
- First, certain publicly visible information from a user’s Houzz profile only if the user made this information publicly available (e.g., first name, last name, city, state, country, profile description) were exposed
- Second, some internal identifiers and fields that have no discernible meaning to anyone outside of Houzz (e.g., country of site used, whether a user has a profile image) were exposed
- Lastly, some internal account information (such as email addresses, user IDs, prior Houzz usernames, one-way encrypted passwords salted uniquely per user, IP addresses, and city and ZIP code data inferred from IP address) and certain publicly available account information (e.g., current Houzz username and, if a user logs into Houzz through Facebook, the user’s public Facebook ID) was exposed
I’ll continue to update this post as the situation develops, however, a breach of this scale once again reinforces the fact that everyone should be using unique and secure passwords across all of their networks and services. For those who are prone to losing their passwords or don’t want to write them down, a password management tool like 1Password offers convenience and security for a low monthly price. 1Password pricing starts as low as just $2.99 for a personal account or $4.99 for a family account.
If you’ve received this notice from Houzz, be sure to reset your password at your earliest convenience to keep your information safe!
Was This Helpful?
If so, please consider making a donation - your support allows me to continue putting out content like this!



